It all starts with a bad sock puppet
If you have problems with Norton 360 or Norton Antivirus, please do not call +1-844-947-4746. You might end up with malware on your computer.
Do you have a look at the accounts that connect with you on Twitter or Medium? I do, and so does my buddy Sector035. In late April 2019, a new person followed Sector’s blog on Medium and he had a look at this new follower.

A weird URL? A nice picture of a female named Pierre? This profile was begging for further research. The URL led to a tech-support site that listed the following phone number: +1-844-947-4746. Sector didn’t even wait to check this number on his computer and immediately googled it on his cell phone. I guess that’s what you call OSINT curious.

It turns out that this phone number was listed on numerous obviously fake sites and blog posts offering tech-support. Out of curiosity, we decided to take a closer look at some of the sites, in order to see how they were connected to each other and possibly find out who was responsible for creating them. At the time we had no idea how time consuming and big this project would be! Among the sites using the phone number, we initially concentrated on these four:

Each site looked worse than the other. Horrible design, bad English and next to the aforementioned phone number, they all used the same address:

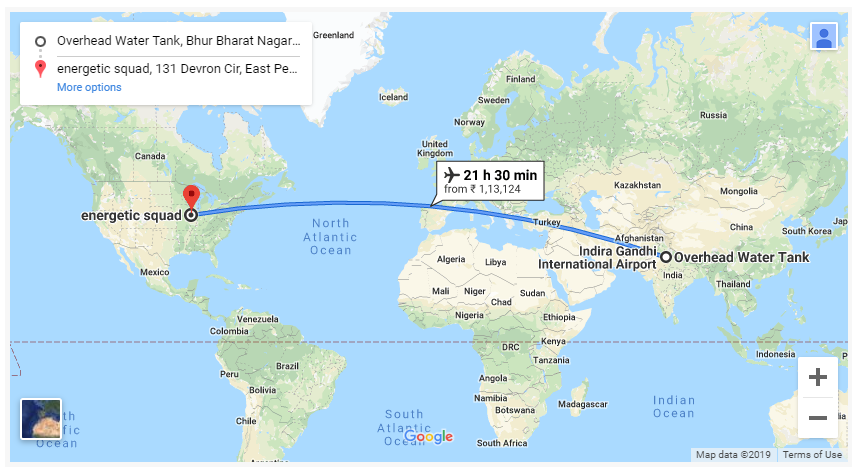
While Sector started to check the WHOIS information using DomainBigData, GoDaddy and Whoxy, I looked into to Google Street View and did a little reverse image searching on the photos. It turns out that all the photos used were either stock pictures or stolen off other people’s social media profiles and the address itself was in an inconspicuous housing area. Googling the address led us to more suspicious sites, some of them using a different phone number. Among these was one belonging to a company allegedly called Energetics Squad LLC. No records existed for such a company in the State of Illinois, nor in any other state. Keep this company in mind, as it will show up in a later blog post as well!
The WHOIS check didn’t always provide the exact name of the registrant, but we found another similarity: most of the websites had been registered around March 13-14, 2019 in India.

Using DNSLytics, Sector also checked the Google Analytics ID and found that the sites were not only linked by all of what was described above, they also shared a common tracking code (UA-code). At this point, it was time to start linking the information in Maltego.
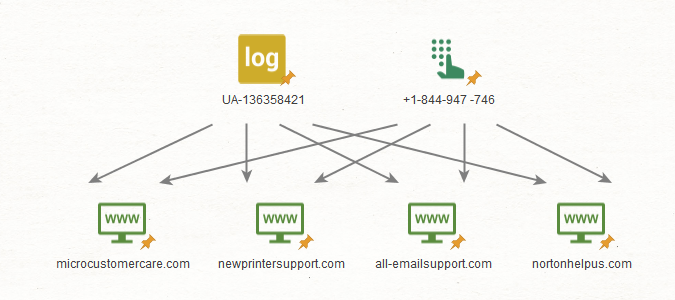
What started with a bad sock puppet, led to googling information and from there to a deep dive into domain data, Google Analytics research, as well as pulling corporate records from official state registries. The hunt was on and upon finding all this correlating data, we couldn’t just let go and decided to push forward.
The Art of OSINT
Art is often considered the process or product of deliberately arranging elements in a way that appeals to the senses or emotions. OSINT is art and sometimes OSINT produces art.
This is big! We collected information on hundreds of different entities; including websites, names, phone numbers, email addresses and much more. When we started, relevant data was just dumped into a text file. To give you an overview of how much we collected and how much time and effort we spent on this project, Sector put together a little infographic.

We also used Hunchly during our collection and then realized we needed to structure the most important data and moved on to a spreadsheet. This worked for a while, until we felt the need to display links between entities in an easy and understandable way. A more visual approach was chosen, and Sector started what I call “The Art of OSINT”: a link chart.
Sector used Maltego for our case, but there are many alternatives you can use as well. I have grown fond of draw.io and others might use one of the various mind mapping apps and platforms. The idea behind link analysis in general is to evaluate relations and connections between entities. Link charts are the visualization of this data, which in many cases make it easier for an analyst to discover connections. Sometimes the connections are not direct, but indirect, linking entities to each other by a third-party individual.
Let us take a look at how link charts can be built from scratch. I previously mentioned a screenshot of one of the scam sites.

This site already has multiple pieces of information that can be connected. A name, a postal address, a phone number and lastly an email address. Each of these is the starting point for further OSINT investigtions. We found that the email address was used to register the domain allbagmanufacturing(dot)com. This domain also lists an Indian phone number in the WHOIS data.

It turns out, that the Indian phone number was also used to register the site roadrunneremailsupports(dot)com.

In conclusion, both sites are likely connected. However, how do we know that this phone isn’t just a burner phone or a random phone number? More OSINT research is required to verify if the phone number is existent and who it belongs to. I also mentioned a little social engineering coming up, didn’t I? If you were hoping to read about this topic now, I have to disappoint you. Rest assured, we have a nice story on social engineering later on. Now, let’s get back to our link analysis.
One piece of information leads to another and soon we find new leads and many connections between the entities. The chart itself has grown quite a bit in the meantime. At first glance, it will seem a bit chaotic. However, it is still easier to handle than relaying this information in a text-based form. For me, link charts have an artistic character. Each chart, whether built manually or automated, is one of a kind. Unique data, unique arrangements, all coming together to form a piece of modern art.

Put this on a large canvas, have Sector sign it and it would be something that could be found in the Guggenheim Museum of Modern Art. One day I plan to do exactly that. A vernissage on “The Art of OSINT”. Until then, let’s keep creating more masterpieces with our online investigations and link charts.
What’s the big deal? And who’s to blame?
Not all information can be found using OSINT. Sometimes a little social engineering can be useful.
We warned you not to call a certain phone number linked to multiple scam sites. So, what exactly happens if you call +1-844-947-4746? Although it was obvious that the sites we were looking at and this phone number were involved in some kind of scam, I was curious to see what the exact business model was. Before making the call, I googled a bit and found out that the number was toll-free in the US. After topping one of my burner phones, I dialed the number.
It rang shortly and a gentleman with an Indian accent answered and asked which kind of assistance I required. I explained that I had problems with Norton 360. I couldn’t activate it. The gentleman wanted my name and my phone number, upon which I provided him with some bogus data. At first, he asked if I was able to install software, as he wanted to use Supremo to check my computer. Playing dumb, I just told him that I didn’t understand what he wanted me to do and that I have never personally installed anything on this computer. My son always did all the IT-stuff for me.
Next up, he mentioned two URLs that I should try to visit: helpme(dot)net and 1234computer(dot)com. It turns out that both sites were also meant to give him remote access to my computer.

This is where another important lesson in OSINT (and life) can be learned: Proper preparation prevents poor performance! I had not expected this and therefore hadn’t set up a clean Windows VM to play around with. Sadly, I had to find an excuse why I couldn’t access the URLs he had cited. I promised to call back, but never managed to get through again. From there on, the number only redirected me to voicemail. Funny enough, the mailbox mentions a typical American name as the owner. Maybe this could be useful in the future.
In any case, it was clear how the scam worked. Unsuspecting, non-tech-savvy users would call the hotline and give the scammers remote access to their computers. From there on, the possibilities to do harm are countless. Ever since then, I have always made sure to have a clean Windows VM that I can use in such cases.
Since we now had an idea what the scam was about, we decided to push forward with our investigations. Sector found a phone number associated with the site energeticsquad(dot)com. This site belonged to an IT-company named Energetic Squad LLC in Illinois, which coincidentally was also located at the address we had already seen on multiple scamming sites. The number found by Sector was an Indian mobile and I decided to get in touch with this person to find out if he or she was in any way related to the aforementioned website or any of the other scam sites. I noticed that it was registered in WhatsApp, so I decided to have a little chat. Of course, I used a burner phone for this; to be more precise, I was running WhatsApp in an Android VM on my computer.

What struck me here, is that I was indeed on the right track. I never said that the company was a LLC, yet it was immediately mentioned by the person I was texting with. By this, the owner of the Illinois company offering local tech-support was using an Indian phone number. He wasn’t keen on giving me his name, but his reactions showed that me that the name I had was also likely correct. At least he didn’t deny it.

I offered to buy his domain and we went back and forth regarding the price. I was pushing hard, something I usually wouldn’t do in a real case, and soon he asked if I could come to the US for further negotiations. I assume he was just trying to put me off track and distracting from the fact that he was actually located in India. His English also wasn’t what I would expect from a native speaker. Of course, I was able to travel to the US and at this point he decided to end the conversation.

Being blocked by a scammer, because he accuses you of being a scammer. Now there’s a pot calling the kettle black! Of course, I burned bridges here and wasn’t able to reestablish contact after this. However, we did learn that the Indian mobile phone number was in fact connected to the website and the company. Also, we had likely found an actual name. Later on, we found out that the company Energetic Squad LLC had been registered in Illinois in the meantime, and that the name of their manager was the same name that is being used on the fake tech support voicemail. Everything and everyone is linked!
There were several other suspects which we had also contacted, and almost everyone acted as suspicious as the person I wanted to buy the domain from. In any case, these conversations gave us many new leads to follow up on and had us pivot toward social media profiles. Maybe these will provide some insight on the scam network.
The more, the better
What are backlinks and how are they used in the Norton scam? Our OSINT investigations lead us into the world of SEO.
The project started with a fake profile on Medium, which led us to several scam websites claiming to provide tech support. While the total number of these sites hasn’t risen much over the past months, entries promoting this scam on blogs, social media profiles and in comments on other websites have drastically risen. We see this as a crude search engine optimization (SEO) attempt.
Throughout the investigations we found individuals specializing in SEO, who where also likely linked to the network we were tracking. One of the sites that popped up in our search was yahoophonesupports(dot)com. Unlike previous fake sites that used Indian addresses and fake English-named personas, such as Nancy Wilson or Steven Dalton, this one was registered by someone named Jiya with a real looking email address. We had narrowed down our search to the city of Noida in India and the phone number used to register the site was definitely linked to our scam network. While most names used to register domains clearly came from fictitious peoples, maybe this was one was real.

Searching for the name on Google led to a result that fits the picture: Jiya from Noida offering SEO services.

Jiya mentions backlinks and blogger outreach, something we have seen in our scam as well. Let me explain the concept of backlinks, also known as inbound links. A backlink is a link on page A referring to page B. Most search engines interpret backlinks as votes on the popularity of a website. So, the more backlinks that lead to page B, the more popular this page seems and thus it will be rated higher in search results. The easiest way to create cheap backlinks is using free blogs, for example Medium. Googling the phone number used in this scam, we come up with over 1.000 Medium posts and sites, each also containing the link to one of the fake support sites, such as nortonhelpus(dot)com.
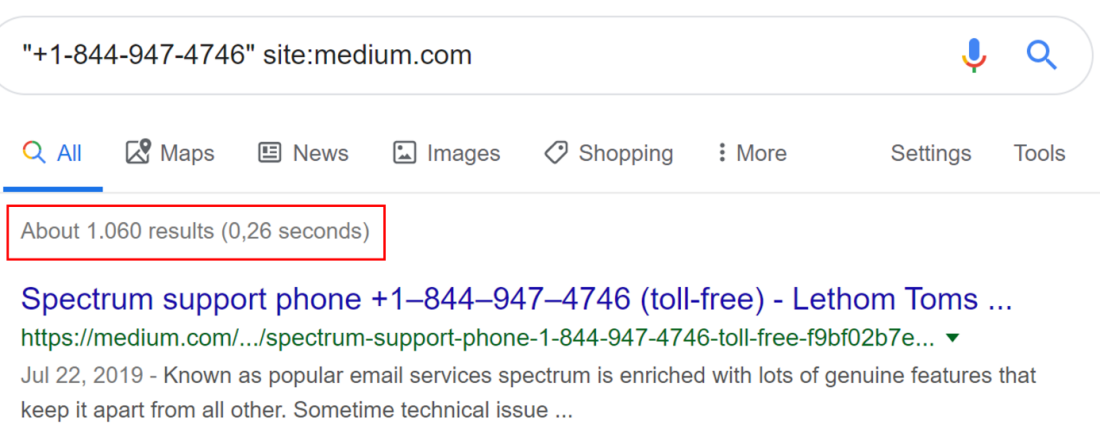
We are not only seeing this on Medium, but across many platforms. The amount of backlinks created clearly indicates that we are dealing with a large team of people, as this is probably not possible by one person or a small team alone. The number of search results for the phone number shown above has risen from 4,000 in May to about 21,000 this week and is still rising!
Of course, most posts come from obvious sock puppets, created with fake names and stolen profile pictures. Here’s Brad Pitt, alias James Rocky, offering tech support.

Once these sites are set up, clicking on the links can be automated, so that the target website (in this case all-emailsupport(dot)com) receives traffic, basically boosting its search index rating. The scam network is not expecting to generate any phone calls or support requests from these obviously fake Medium sites, these are just used in the SEO process for the actual scam site. We have been seeing these SEO-enablers on Twitter, Issuu and basically any platform that allows you to post information “quick and dirty”.
During our project we also looked at Google Trends, to figure out where the main targets of this scam were likely located. Obviously in the US, as the main tech support phone numbers were US toll-free numbers. However, we also noticed a British phone number. Google Trends allows you to look up search terms and see the interest over time and the region of interest for that specific search term. We were curious to see if any notable searches on one of the scam topics was googled in the UK often. We checked “activate Norton”, since this was one of the main services the scam network was allegedly offering: activating an expired Norton account.
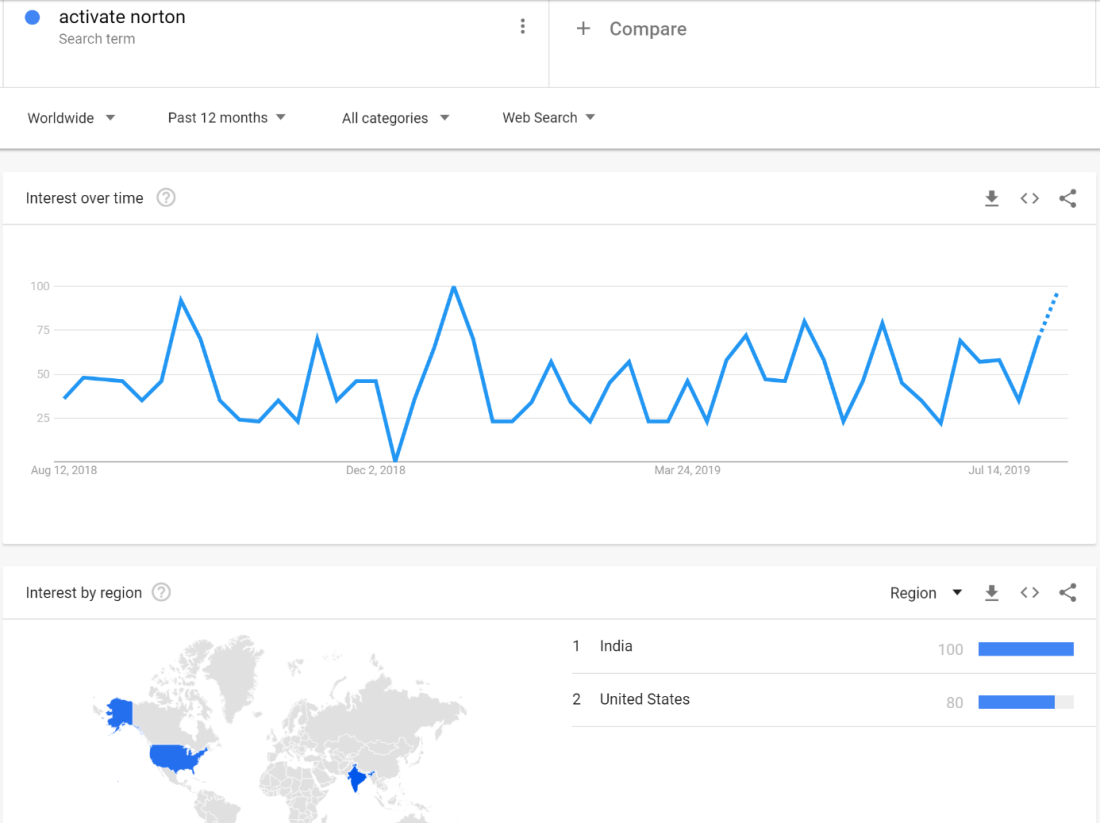
Sure enough, the main regions that googled this term were the US and India. The US is obvious. This is the market the scammers are targeting. But why does India rank higher? One explanation could be testing the search term during the SEO-process. Coincidently, some of the peaks in the interest over time relate to time periods in which new fake sites were created. No notable searches were seen coming from the UK.
As mentioned before, most of the bogus blog posts were created really sloppy, as their sole purpose was to generate backlinks. We also found several sites linked to this scam that were apparently selling software. A lot of these sites were created using predefined templates, in some cases showing the shipping time or the general location on a map.

Apparently, the creator of this site had his location (likely based on a geolocation through Google) automatically added and didn’t bother to change it before putting the site online. In any case, he achieved his goal: A backlink to a scam site.
Now that we’ve learned how this scam uses SEO to promote their wrongdoings, is there anything that can be done to effectively tamper this scam network? How about Google, Bing, Yahoo and other major search engines take any site off their listing that features “+1-844-947-4746”. Except ours, we’re the good guys!
Mistakes on social media
Never be too careless with what you post on social media. It might come back to haunt you one day and in the case of our investigations it sure led to some key findings on the scam network!
The ultimate goal of our investigation was to find the people behind the scam. We had found fake personas and most of the WHOIS data was misleading as well. Of all the people we came across, there was still a reasonable amount of doubt that they were actually involved in the scam, or we couldn’t reveal their true identities for sure. In our hunt for the truth we also turned to social media, hoping to find someone connected to our case.
As previously mentioned, most names used to register websites were clearly fake. Nancy Wilson and Steve Dalton were among the favorites. However, we did notice that the majority of sites had Indian addresses in the WHOIS data. In particular, two addresses reoccurred often: one in Noida and one in Gurgaon (also known as Gurugram). We decided to find Facebook profiles that had visited both cities and that were also linked to East Peoria, the city in Illinois that the scammers posted on their websites. Maybe someone was careless enough and had checked into all three places. Of course, this was done a while back when the Facebook graph search was still working.
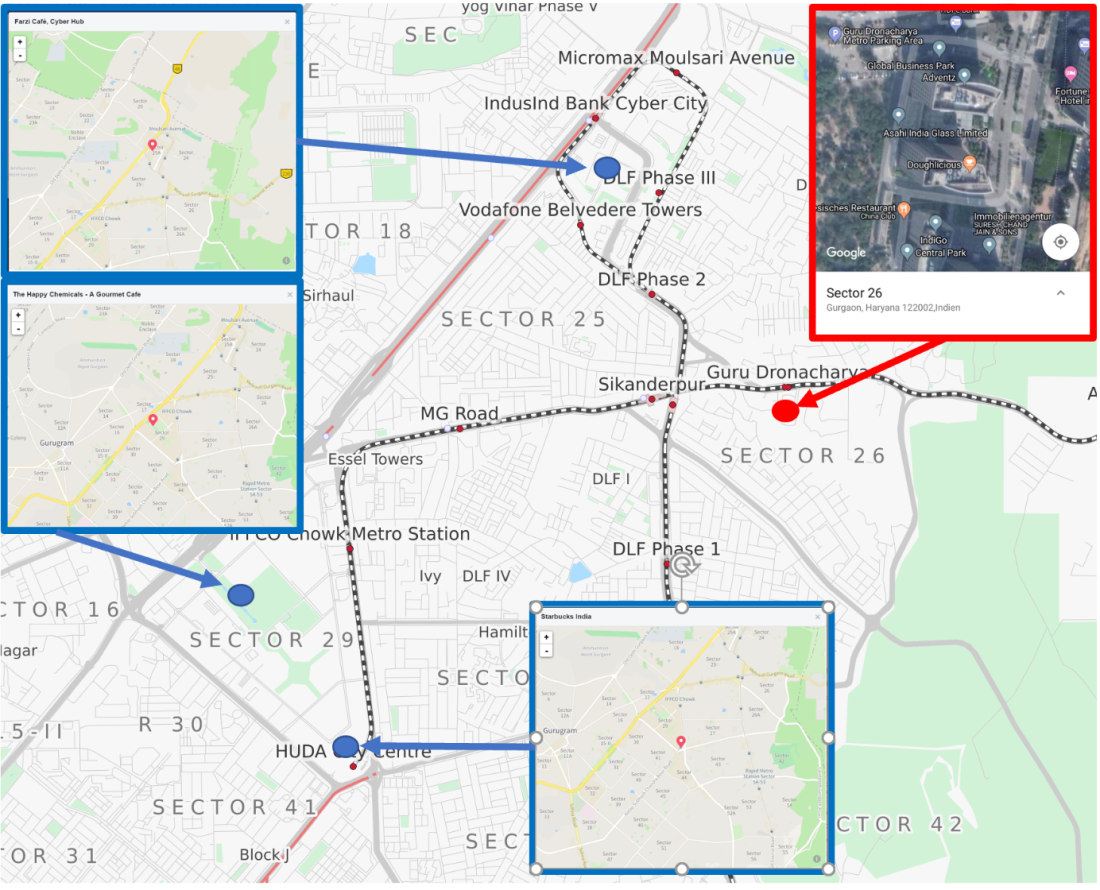
Jackpot! While we hadn’t expected to find anything on this wild query, one Facebook profile matched our search. This person, named Baljeet, was a very active social media user and constantly checked into places on Facebook. Among these check-ins were Noida, Gurgaon and East Peoria.

Intelligence collection always feeds on mistakes your adversaries or intelligence targets make, and Baljeet committed a major blunder here. Soon after, we found ourselves digging into Baljeet’s profile. It turns out, that he had frequently visited locations (marked in blue) in the vicinity of the office building (marked in red) which was found in the WHOIS data of the scam sites and in which we suspected the team of developers behind these sites to be located.

At the same time, we discovered that Baljeet registered a website with his full name and actual email address, which we had found in his Twitter timeline. This website was providing web design services to customers in the US. And guess what? The site was using the same address in East Peoria and also the same phone number as the scam sites! I decided to have a little chat with Baljeet on Facebook to confront him with this information.

The conversation went on for a while and Baljeet kept coming up with excuses and dodgy information on why his website was using the same address and phone number as the scam sites. After our talks, he actually took down both for a while, but the address is back on the website today. To us it is clear: Baljeet is definitely involved in this scam. You don’t just sit in India and coincidently use the same address (in the middle of nowhere) and phone number as multiple scam sites on your own site. You don’t just coincidently happen to work in vicinity of addresses we have attributed to the scam sites.
While looking into other social media profiles used by Baljeet, we came across other indicators that fit the overall picture. A couple days ago, he proudly posted the following on Twitter: A certificate of an advanced Google Analytics course (my browser was set to German when I opened the link).

As you can see, the information we won from social media research led to us a prime suspect in our case. Not only did we have a real name now, we also had a unique username, a pattern of life and enough information to verify his involvement in our scam.
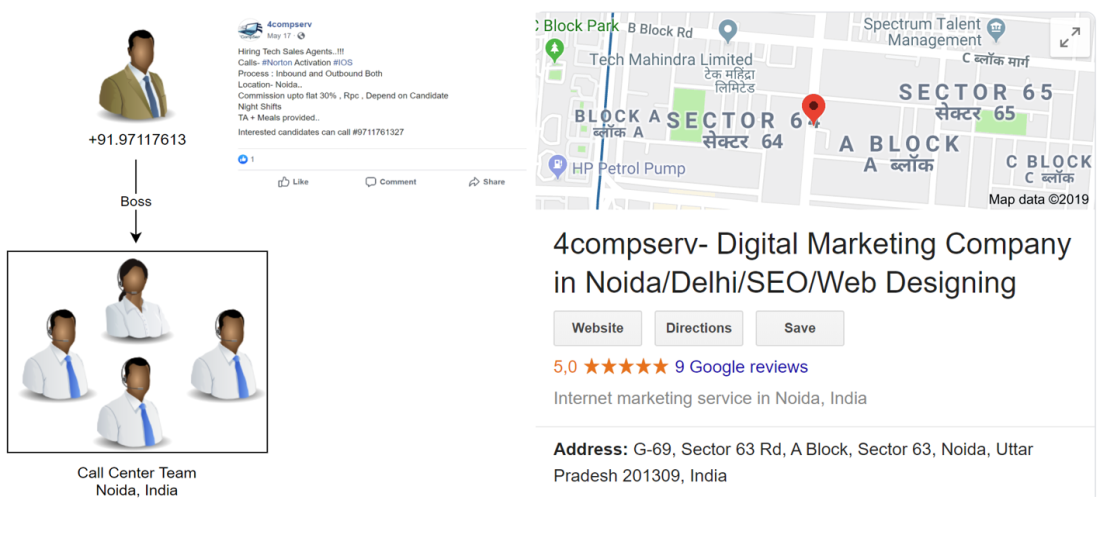
Our social media research also led to many more key findings. One of the phone numbers we found in the scam sites’ WHOIS data was also posting job advertisements on Facebook.

A call center agent providing support to activate Norton? That’s exactly how our hunt started. Looks like it is all coming together! The information we gathered throughout our social media research was invaluable and had us dig even deeper into WHOIS data and source code from the scam websites, leading to unravelling the whole network behind it.
Tracing ownership
All roads lead to Rome. Or in our case to the Indian city of Noida and a certain phone number we found when we used Google Drive API and RiskIQ to generate more leads in our investigations of the Norton scam.
Above, we have shown you how we identified a possible scammer, visualized connections, contacted scammers and how they are using SEO to boost the ranking of their websites within search results. Here, we explain how we used several tools and techniques to connect the different domains and information, ultimately leading to a single person that sits in the middle of the web like a spider. Is it Baljeet, who was mentioned in the previously? Or are there more people working on this scam?
To answer that question, we went back to the beginning of our investigations and revisited the URL where it all started, the “nortonhelpus[dot]com” site. The website is not just a page that displays the scam phone number, it also contains a link that leads to a subdomain: “activate.nortonhelpus[dot]com”. Here we found two separate links to Norton software placed on a Google Drive.

The person uploadeding this was apparently “Nancy Wilson”, coincidentally the same name as the person who registered the domain name “nortonhelpus[dot]com”. With a common name like this, there wasn’t a lot we could do. We needed to find out what email address was connected to the Google account used, and who was in control of it.
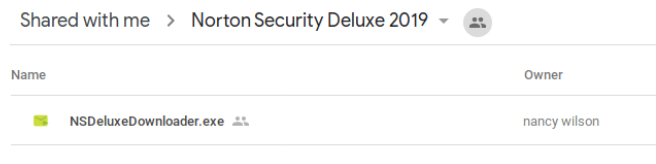
The email within the Whois information for “nortonhelpus[dot]com” was “nw815624@gmail.com”, and to see whether this was the same email address used to upload the files, we had to find out who the actual owner of the Google Drive was. There are two ways of retrieving that kind of information. The first one involves using Firefox and opening up the Developer mode by pressing F12 after loading the page and then clicking on the Inspector. We searched for “@gmail.com” and were presented with a few options. While going over these options, we found the email address of the user hidden somewhere in the source code of the page.

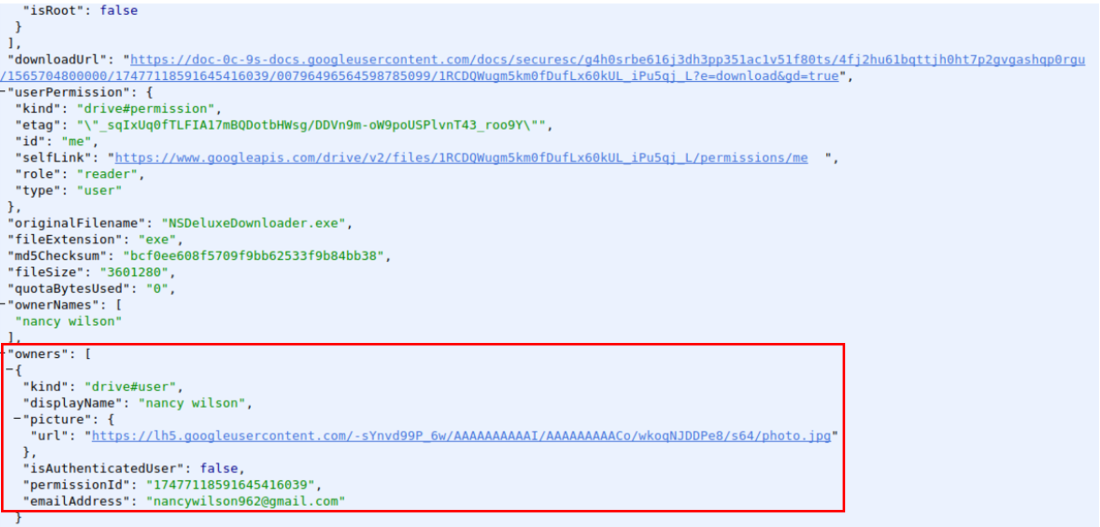
If the owner’s email address cannot be found in the source code of the site, there is another way to move forward: the official Google Drive API. While using the older v2 version instead of the newer and currently active API v3, we were be able to retrieve information on the owner of said Google Drive, including an email address. The specific endpoint we needed to query was “drive.files.get”. After creating a developer account and a temporary project, and by using the online test form (https://developers.google.com/apis-explorer/#p/drive/v2/drive.files.get), we were able to query the endpoint and retrieve all the metadata of the uploaded files. The email address of “Nancy Wilson”, who we know is a fake persona.
Using the following command on the Google drive we were investigating, it pulls the results shown below.
Command: GET https://www.googleapis.com/drive/v2/files/1RCDQWugm5km0fDufLx60kUL_iPu5qj_L?key={YOUR_API_KEY}
Result:

Finding the email address “nancywilson962@gmail.com” gave us a new entry to start searching online for any information that could lead to the person behind the website. For this we turned to RiskIQ, where we used the PassiveTotal platform to query their massive data set of historical Whois information. Within RiskIQ you have the option to search on domain names, but also on email addresses or phone numbers that are inside the Whois registration information, which makes it extremely suitable to trace scammers via domain registration. When searching for the email address we sadly found out that only one domain was registered, the domain “amazing-wash[dot]com”. It appeared to be registered in India by a person called “Ramesh Kumar”, according to the Whois information he was living in Noida and with all this information we found a new phone number.
Though we hoped to find more domain names with our initial query, we simply pivoted on this phone number within RiskIQ for more mentions of it. And that is when we hit the jackpot.

There were more than a dozen domains connected to this single phone number. Even though we already found multiple domain names by searching for websites mentioning the phone number +1-844-947-4746 or using the address in East Peoria, all this information was connected via Whois information through a single phone number that had direct leads to the person placing the files on Google Drive. It was time to pivot again, this time on each and every phone number and email address that we found in the Whois information of all the domains. Upon finding new information, we retrieved related new domains too and so on and so forth. By using RiskIQ, manual Whois queries and going over the content of the websites, we were massively expanding the list of entities in our investigation. Starting with about 100 entities after our initial Google searches and manual labor, to well over 200 items by using the information within RiskIQ! This is how we ended up with a very large cluster of websites, fake aliases and email addresses, a bunch of new phone numbers, all circling around a person called “Ramesh Kumar”. The person with the phone number that connects more than 75% of all the collected data in this investigation in a direct or indirect way.

Of course, we couldn’t resist and tried to call Ramesh on the phone number we had discovered. After these calls, everything made total sense and we pretty much figured out how this whole network of scammers works.
Putting the pieces together
Gotcha! We found out who is responsible for this massive scam. Using OSINT and social engineering we tracked down the company behind the Norton Scam.
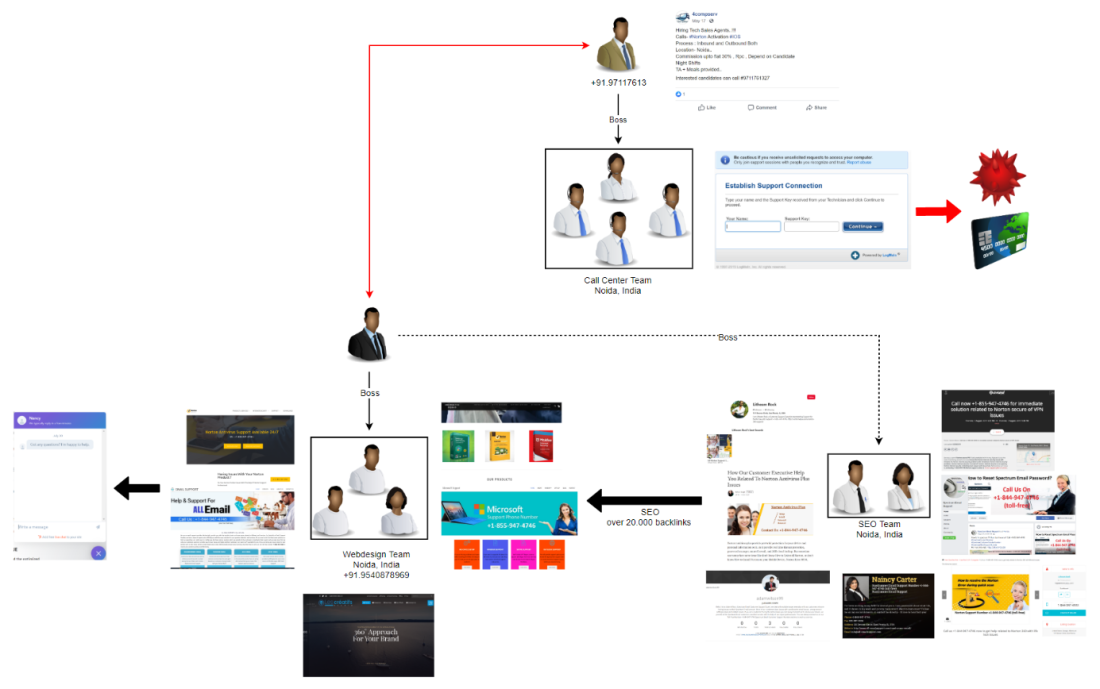
Time to finally unravel the Norton scam. Sector and I have decided to conclude our investigations and put the pieces together, after spending countless hours working on this case. Every time we thought we had figured it out, new information was found, taking us down another rabbit hole. Sometimes we spent days following a lead, just to find out that it wasn’t related to our case at all. As with most investigations, we were not able to solve all mysteries, but we are pretty sure we identified the company and some individuals behind this massive scam scheme.
We pointed out how everything led to specific Indian phone number (+91.9540878969). This number was used to register many of the domains we were looking into. Once more, I decided to make some phone calls to India. I found out that the number belongs to a web design office. The first four phone calls were answered by different men who did not understand English, so they hung up on me. My fifth phone call was more successful. I got a hold of a woman named Priya and told her that a friend of mine had recommend them and that I was looking to have a website set up for me. I had called the right place and I would need to speak to her boss, Priya explained. I also mentioned that the site was to be used as a scam site to obtain credit card data. This too was possible according to Priya. Soon afterwards I had a conversation with the boss, who remained nameless. If I was willing to pay roughly 150$ on PayPal, they would set up the site I needed. With these phone calls, we have proven that the web design office was responsible for setting up the type of scam sites that we have seen throughout our investigations.

During our research, we also came across a site which offered web design services to US customers and to which we had actually found legit websites they had created. This is something very common: using a US frontend to sell IT-services that are performed in India. So, not everything the team did was illegal or scam-related.

In order to promote the scam sites, another team was responsible for search engine optimization (SEO). The SEO team was most likely also located in the offices of the web design team, probably under the same leadership. Their job is to flood the internet with backlinks in order to promote the scam sites. So far, we have found more than 20,000 entries for this cause. From Facebook posts, to Medium blogs, to comments on non-related webpages; a large variety of backlinks were created in the past year.

The purpose of the scam is have the victims call one of the tech support phone numbers. Thus, a team of call center agents is required. Remember how the scam works? If an unsuspecting victim calls the number, they provide ‘assistance’ by obtaining remote access to the victim’s computer. In some cases malware is installed, in other cases they ask for credit card data in order to bill the customers for their service.
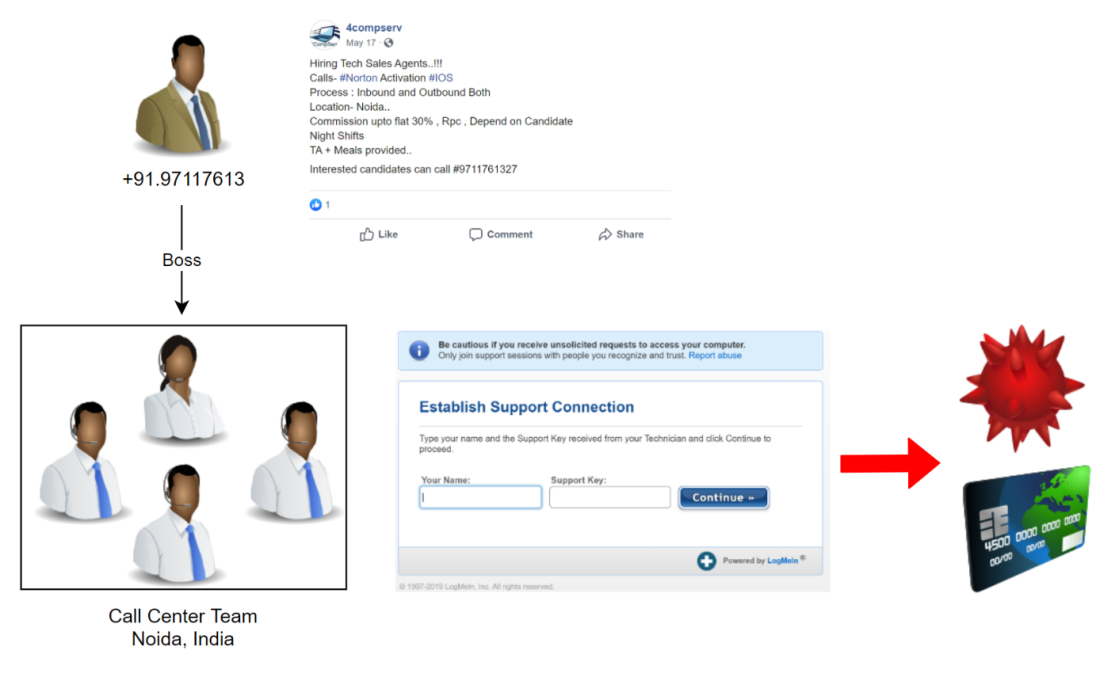
These call center agents were hired by a company named 4compserv, which is located at an address that was also used to register some of the identified scam domains. We suspect this is root of all evil, the company behind the scheme. Or at least some employees of the company, since we have also found evidence of 4compserv conducts legal business as well.
More evidence came up, which proves that the web design office and the call center are definitely related. Shortly after I had spoken to the boss of the web design office, I received a phone call from the number linked to the call center (+91.97117613). Unfortunately, I missed the call and haven’t been able to reach them ever since. Furthermore, one of the scammers I had personally texted with recently updated the CV on his website. Have a look at his current jobs:

While there are still some questions to be answered, our research has enabled us to have an overall understanding of the network and the techniques used to run their scam, as well as identifying the company most likely behind this scam: 4compserv in Noida, India.
Along the way, we would often stumble upon funny facts. Some of the scam developers were just so sanguine, they didn’t want to obscure their tracks. Such as the preferred use of the name ‘Nancy Wilson’ to register domains or create sock puppets. The original websites the scammers had set up were very crude, now it seems they are using nice looking WordPress templates, including chatbots. Usually, the chatbot would ask for a phone number, so the scammers can call back. And guess who you would be chatting with on all of these sites? Good ol’ Nancy!

We’re done! We managed to find the perpetrators behind all this. What started with a sock puppet on Medium led to unravelling a largescale scam network, targeting unsuspecting victims seeking tech support. We hope that our project may help counter the threat originating from this specific scam and raise awareness for similar schemes. Also, thanks to many of our readers for sharing the posts from this series on Twitter and LinkedIn, ultimately ranking the articles higher and higher on Google. Using OSINT and social engineering to enable counter-SEO against the scammer’s massive SEO effort!
Now it’s time to relax a bit…before we start the next awesome project!
Sector035/MW-OSINT – 28.08.2019
We explicitly decided to keep the disclosure of personal information on the investigated individuals to a minimum in these blog posts. However, the complete information gathered is available to law enforcement and/or the companies targeted by this scam upon request.